As the Internet of Things (IoT) continues to transform industries worldwide, the need for robust security frameworks has become more critical than ever. From smart homes and healthcare systems to industrial automation and connected vehicles, billions of IoT devices are exchanging sensitive data every second. This rapid expansion has created new cybersecurity challenges, making IoT Identity and Access Management (IAM) an essential solution for modern enterprises.
Innovation and collaboration are now driving the growth of the global IoT IAM market. Organizations are investing significantly in advanced technologies such as Artificial Intelligence (AI), Machine Learning (ML), and automation to strengthen access controls and improve threat detection. These innovations are helping businesses secure connected ecosystems while ensuring scalability, interoperability, and regulatory compliance.
What is IoT Identity and Access Management?
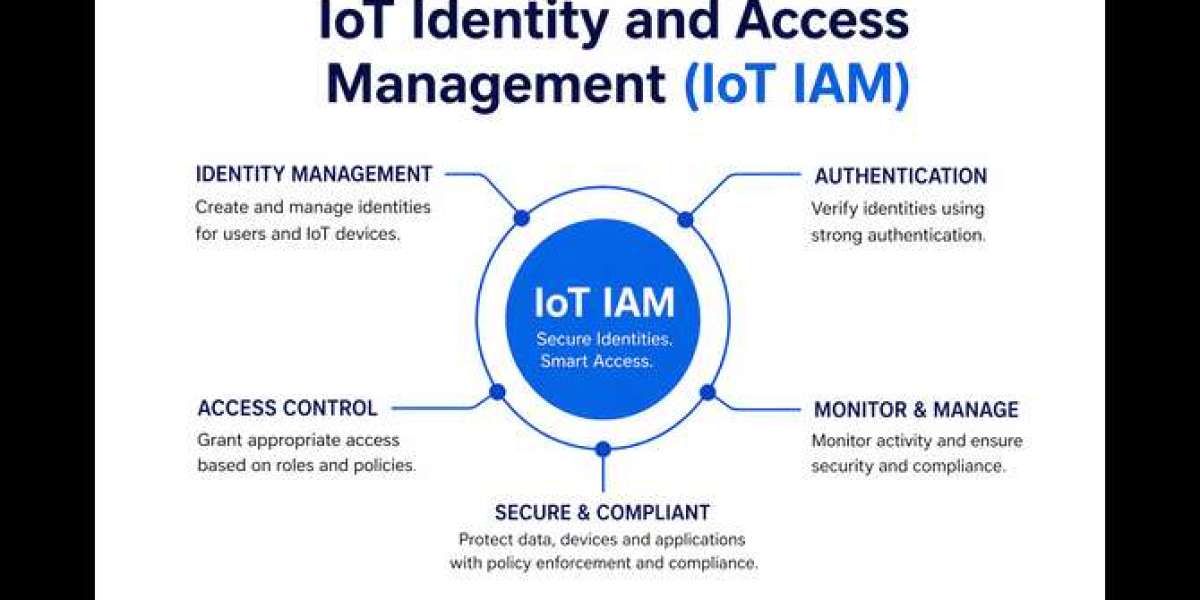
IoT Identity and Access Management (IAM) refers to the framework of policies, technologies, and processes used to manage digital identities and control access for IoT devices, users, applications, and systems. Unlike traditional IAM systems designed primarily for human users, IoT IAM focuses on securing machine identities and enabling trusted communication between connected devices.
The goal of IoT IAM is to ensure that only authorized devices and users can access networks, applications, and sensitive data, thereby reducing the risk of cyberattacks, unauthorized access, and data breaches.
Why IoT IAM is Essential for Modern Businesses
As organizations increasingly adopt IoT technologies, the attack surface expands significantly. Every connected device represents a potential entry point for cybercriminals. Without a strong IoT IAM strategy, businesses face risks such as:
- Unauthorized device access
- Data leakage and privacy breaches
- Device tampering and manipulation
- Malware attacks and ransomware
- Compliance violations under GDPR, CCPA, HIPAA, and other regulations
Implementing a robust IAM solution helps organizations reduce these risks while maintaining operational efficiency and customer trust.
Key Features of IoT IAM Solutions
- Device Identity Management
Each IoT device requires a unique digital identity to verify authenticity and establish trust. IAM solutions provide secure onboarding, identity provisioning, and lifecycle management for connected devices.
- Authentication and Authorization
Strong authentication mechanisms ensure that only verified users and devices can access systems. Multi-factor authentication (MFA), certificate-based authentication, and Zero Trust security models are becoming standard practices.
- Role-Based Access Control (RBAC)
RBAC helps organizations define and enforce access permissions based on user roles, device functions, and operational requirements. This minimizes unnecessary access and strengthens security.
- AI-Powered Threat Detection
AI and machine learning technologies enable real-time monitoring of user behavior and device activity. Suspicious activities can be detected instantly, allowing faster incident response and reducing security risks.
- Compliance Management
IoT IAM solutions help businesses meet regulatory requirements by providing audit trails, access logs, identity governance, and data protection controls necessary for compliance frameworks.
The Role of AI and Machine Learning in IoT Identity and Access Management (IAM)
Artificial Intelligence and Machine Learning are revolutionizing the IAM landscape by introducing predictive security capabilities. Traditional security systems often rely on reactive measures, but AI-driven IAM solutions can proactively identify anomalies before they escalate into major threats.
Machine learning algorithms analyze patterns across connected devices, detect unusual login attempts, flag suspicious access requests, and automate security responses. This significantly improves the overall security posture of IoT ecosystems.
Importance of Interoperability and Scalability
The global IoT market is growing rapidly, with organizations deploying thousands—even millions—of connected devices across multiple environments. This makes interoperability and scalability critical success factors for IAM solutions.
Interoperability
IoT ecosystems often involve devices from multiple vendors operating across cloud, on-premises, and hybrid infrastructures. IAM solutions must seamlessly integrate with existing systems to ensure consistent security across all platforms.
Scalability
As businesses expand, IAM systems must be capable of managing increasing volumes of identities, devices, and access requests without compromising performance or security.
Organizations that prioritize these capabilities are better positioned for long-term digital transformation success.
Future Trends in the Global IoT IAM Market
The future of IoT Identity and Access Management will be shaped by several emerging trends:
- Zero Trust Architecture adoption
- Passwordless authentication
- Decentralized identity management
- Blockchain-based identity verification
These innovations will further strengthen IoT security while improving operational efficiency and user experience.
Conclusion
Innovation and collaboration remain central to the advancement of the global IoT Identity and Access Management (IAM) market. As cyber threats become more sophisticated, businesses must adopt intelligent, scalable, and compliant IAM solutions to protect their connected ecosystems.
The integration of AI and machine learning is transforming IAM from a reactive security measure into a proactive defense strategy. By focusing on interoperability, scalability, and compliance, organizations can ensure sustainable growth while safeguarding critical assets.